Understanding Policy Association
Network Architecture
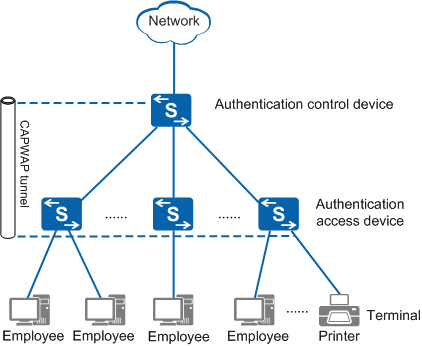
Figure 1 shows the policy association network architecture, which consists of three roles: terminal, authentication access device, and authentication control device.
- Terminal: provides human-machine interfaces for user authentication and resource access. The terminals include PCs, laptops, tablets, and dumb terminals.
- Authentication access device: a policy enforcement point to implement network access policies for users.
- Authentication control device: a policy control point to authenticate users and control their access policies.

Authentication control devices and authentication access devices use control and provisioning of wireless access point (CAPWAP) tunnels to establish connections. In addition, authentication control devices and authentication access devices use CAPWAP tunnels to complete user association, transmit messages, deliver user authorization policies, and synchronize user information.
Implementation
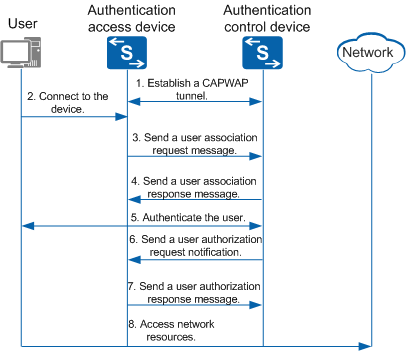
Figure 2 shows the policy association process.
- An authentication control device establishes a CAPWAP tunnel with an authentication access device.
- After detecting the access of a new user, the authentication access device creates a user association table and saves basic information such as the user and access port.
- The authentication access device sends a user association request to the authentication control device.
- The authentication control device creates the user association entry, saves mapping between the user and authentication access device, and sends a user association response to notify the authentication access device of successful association.
- The user initiates an authentication request to the authentication control device. The authentication access device forwards the authentication packet between the user and authentication control device.
- The authentication control device deletes the user association entry. After the authentication succeeds, the authentication control device generates a complete user entry. At the same time, the authentication control device sends a user authorization request notification to the authentication access device, and delivers the network access policy for the user.
- The authentication access device saves the user association entry, enables the specified network access rights for the user, and sends an authorization response to the authentication control device.
- The user accesses the specified network resources.

The preceding process occurs after the CAPWAP tunnel is established between the authentication control device and authentication access device. The establishment step is not mentioned in the previous process.