Example for Configuring Layer 3 IPoE Access (Web Authentication)
This section provides an example for configure Layer 3 IPoE access with web authentication.
Networking Requirements
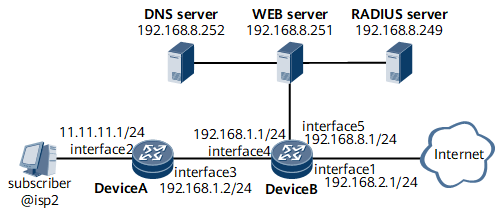
On the network shown in Figure 1, the networking requirements are as follows:
A user belongs to the domain isp2 and connects to GE 0/1/2.1 on Device B through Device A, a DHCP relay agent. The user then accesses the Internet in Layer 3 IPoE access mode.
The user adopts web authentication, Remote Authentication Dial In User Service (RADIUS) authentication, and RADIUS accounting.
The IP address of the RADIUS server is 192.168.8.249. The authentication port number is 1812, and the accounting port number is 1813. The standard RADIUS protocol is used. The shared key is it-is-my-secret1.
The IP address of the DNS server is 192.168.8.252.
The IP address of the web server is 192.168.8.251. The shared key is webvlan.
Configuration Roadmap
The configuration roadmap is as follows (all functions, except DHCP relay, are configured on Device B):
Configure DHCP relay on Device A.
Configure authentication and accounting schemes.
Configure a RADIUS server group.
Configure an IP address pool.
Configure a pre-authentication domain and an authentication domain for web authentication.
Configure a web server.
Configure UCL rules and traffic management policies.
Configure a BAS interface and an uplink interface.
Data Preparation
To complete the configuration, you need the following data:
Authentication scheme name and authentication mode
Accounting scheme name and accounting mode
Name of the RADIUS server group as well as IP addresses and port numbers of the RADIUS authentication server and accounting server
IP address pool name, gateway address, and DNS server address
Domain names
IP address of the web server
UCL rule numbers
Traffic policy names
BAS interface parameters
Procedure
- Assign IP addresses to interfaces on Device A and Device B.
# Assign IP addresses to the interfaces on Device A.
<HUAWEI> system-view [~HUAWEI] sysname DeviceA [*HUAWEI] commit [~DeviceA] interface GigabitEthernet0/1/2 [~DeviceA-GigabitEthernet0/1/2] ip address 10.11.11.1 255.255.255.0 [*DeviceA-GigabitEthernet0/1/2] commit [~DeviceA-GigabitEthernet0/1/2] quit [~DeviceA] interface GigabitEthernet0/1/1.1 [*DeviceA-GigabitEthernet0/1/1.1] commit [~DeviceA-GigabitEthernet0/1/1.1] ip address 192.168.1.2 255.255.255.0 [*DeviceA-GigabitEthernet0/1/1.1] vlan-type dot1q 1 [*DeviceA-GigabitEthernet0/1/1.1] commit [~DeviceA-GigabitEthernet0/1/1.1] quit
# Assign an IP address to the interface on Device B.
<HUAWEI> system-view [~HUAWEI] sysname DeviceB [*HUAWEI] commit [~DeviceB] interface GigabitEthernet0/1/2.1 [*DeviceB-GigabitEthernet0/1/2.1] ip address 192.168.1.1 255.255.255.0 [*DeviceB-GigabitEthernet0/1/2.1] vlan-type dot1q 1 [*DeviceB-GigabitEthernet0/1/2.1] commit [~DeviceB-GigabitEthernet0/1/2.1] quit
- Configure DHCP relay on Device A.
[~DeviceA] interface GigabitEthernet0/1/2 [*DeviceA-GigabitEthernet0/1/2] dhcp select relay [*DeviceA-GigabitEthernet0/1/2] ip relay address 192.168.1.1 [*DeviceA-GigabitEthernet0/1/2] commit [~DeviceA-GigabitEthernet0/1/2] quit
- Configure a network-side IP address pool on Device B. The gateway address of the IP address pool must be on the same network segment as the IP address of the inbound interface on Device A, the DHCP relay agent.
[~DeviceB] ip pool huawei bas local [*DeviceB-ip-pool-huawei] gateway 10.11.11.1 24 [*DeviceB-ip-pool-huawei] commit [~DeviceB-ip-pool-huawei] section 0 10.11.11.2 10.11.11.255 [~DeviceB-ip-pool-huawei] dns-server 192.168.8.252 [*DeviceB-ip-pool-huawei] commit [~DeviceB-ip-pool-huawei] quit
- Configure AAA schemes.
# Configure an authentication scheme.
[~DeviceB] aaa [~DeviceB-aaa] authentication-scheme auth2 [*DeviceB-aaa-authen-auth2] authentication-mode radius [*DeviceB-aaa-authen-auth2] commit [~DeviceB-aaa-authen-auth2] quit
# Configure an accounting scheme.
[~DeviceB-aaa] accounting-scheme acct2 [~DeviceB-aaa-accounting-acct2] accounting-mode radius [*DeviceB-aaa-accounting-acct2] commit [~DeviceB-aaa-accounting-acct2] quit [~DeviceB-aaa] quit
- Configure a RADIUS server group.
[~DeviceB] radius-server group rd2 [*DeviceB-radius-rd2] radius-server authentication 192.168.8.249 1812 [*DeviceB-radius-rd2] radius-server accounting 192.168.8.249 1813 [*DeviceB-radius-rd2] radius-server type standard [*DeviceB-radius-rd2] radius-server shared-key-cipher it-is-my-secret1 [*DeviceB-radius-rd2] commit [~DeviceB-radius-rd2] quit
- Configure domains.
# Configure a domain named default0 to be the pre-authentication domain for web authentication.
[~DeviceB] user-group huawei [~DeviceB] aaa [~DeviceB-aaa] domain default0 [*DeviceB-aaa] commit [~DeviceB-aaa-domain-default0] user-group huawei [~DeviceB-aaa-domain-default0] web-server 192.168.8.251 [~DeviceB-aaa-domain-default0] web-server url http://192.168.8.251 [~DeviceB-aaa-domain-default0] ip-pool huawei [~DeviceB-aaa-domain-default0] quit
# Configure a domain named isp2 to be the authentication domain for web authentication.
[~DeviceB-aaa] domain isp2 [*DeviceB-aaa-domain-isp2] authentication-scheme auth2 [*DeviceB-aaa-domain-isp2] accounting-scheme acct2 [*DeviceB-aaa-domain-isp2] radius-server group rd2 [*DeviceB-aaa-domain-isp2] commit [~DeviceB-aaa-domain-isp2] quit [~DeviceB-aaa] quit
- Configure an IP address used by the device to receive portal packets from the web authentication server.
[~DeviceB] web-auth-server source-ip 192.168.8.1
- Configure a web server.
[~DeviceB] web-auth-server enable [*DeviceB] commit [~DeviceB] web-auth-server 192.168.8.251 key cipher webvlan
- Configure UCLs.
# Configure UCL rules.
[~DeviceB] acl 6000 [*DeviceB-acl-ucl-6000] rule 10 permit ip source user-group huawei destination ip-address 127.0.0.1 0 [*DeviceB-acl-ucl-6000] rule 15 permit ip source ip-address 127.0.0.1 0 destination user-group huawei

In this example, configuring the UCL for 127.0.0.1 is an example for pre-authentication domain users to access a specific website. After the preceding UCL for 127.0.0.1 is configured, user packets sent to the CPU of Device B can pass through, and pre-authentication domain users can access 127.0.0.1.
[*DeviceB-acl-ucl-6000] rule 20 permit ip source user-group huawei destination ip-address 192.168.8.252 0 [*DeviceB-acl-ucl-6000] rule 25 permit ip source ip-address 192.168.8.252 0 destination user-group huawei [*DeviceB-acl-ucl-6000] rule 30 permit ip source user-group huawei destination ip-address 192.168.8.249 0 [*DeviceB-acl-ucl-6000] rule 35 permit ip source ip-address 192.168.8.249 0 destination user-group huawei [*DeviceB-acl-ucl-6000] rule 40 permit ip source user-group huawei destination ip-address 192.168.8.251 0 [*DeviceB-acl-ucl-6000] rule 45 permit ip source ip-address 192.168.8.251 0 destination user-group huawei [*DeviceB-acl-ucl-6000] commit [~DeviceB-acl-ucl-6000] quit [~DeviceB] acl 6001 [*DeviceB-acl-ucl-6001] rule 10 permit tcp source user-group huawei destination-port eq www [*DeviceB-acl-ucl-6001] rule 15 permit tcp source user-group huawei destination-port eq 8080 [*DeviceB-acl-ucl-6001] commit [~DeviceB-acl-ucl-6001] quit
# Configure traffic management policies.
[~DeviceB] traffic classifier web_permit [*DeviceB-classifier-web_permit] if-match acl 6000 [*DeviceB-classifier-web_permit] commit [~DeviceB-classifier-web_permit] quit [~DeviceB] traffic behavior web_permit [*DeviceB-behavior-web_permit] permit [*DeviceB-behavior-web_permit] commit [~DeviceB-behavior-web_permit] quit [~DeviceB] traffic classifier web_deny [*DeviceB-classifier-web_deny] if-match acl 6001 [*DeviceB-classifier-web_deny] commit [~DeviceB-classifier-web_deny] quit [~DeviceB] traffic behavior web_deny [*DeviceB-behavior-web_deny] http-redirect [*DeviceB-behavior-web_deny] commit [~DeviceB-behavior-web_deny] quit [~DeviceB] traffic policy web [*DeviceB-policy-web] classifier web_permit behavior web_permit [*DeviceB-policy-web] classifier web_deny behavior web_deny [*DeviceB-policy-web] commit [~DeviceB-policy-web] quit
# Apply user-side traffic management policies globally.
[~DeviceB] traffic-policy web inbound
- Configure interfaces.
# Configure a BAS interface.
[~DeviceB] interface GigabitEthernet 0/1/2.1 [~DeviceB-GigabitEthernet0/1/2.1] bas [~DeviceB-GigabitEthernet0/1/2.1-bas] access-type layer3-subscriber default-domain pre-authentication default0 authentication isp2

For Layer 3 users that do not obtain IP addresses from Device B, run the layer3-subscriber start-ip-address [ end-ip-address ] [ vpn-instance instance-name ] domain-name domain-name command in the system view to specify the IP address segment on which the Layer 3 users reside and the authentication domain name.
[*DeviceB-GigabitEthernet0/1/1.1-bas] commit [~DeviceB-GigabitEthernet0/1/2.1-bas] quit [~DeviceB-GigabitEthernet0/1/2.1] quit
# Configure an uplink interface.
[~DeviceB] interface GigabitEthernet 0/1/1 [~DeviceB-GigabitEthernet0/1/1] ip address 192.168.2.1 255.255.255.0 [*DeviceB-GigabitEthernet0/1/1] commit [~DeviceB-GigabitEthernet0/1/1] quit
Configuration Files
- Device A configuration file
# sysname DeviceA # interface GigabitEthernet0/1/1.1 vlan-type dot1q 1 ip address 192.168.1.2 255.255.255.0 # interface GigabitEthernet0/1/2 undo shutdown ip address 10.11.11.1 255.255.255.0 dhcp select relay ip relay address 192.168.1.1 # return
Device B configuration file
# sysname DeviceB # radius-server group rd2 radius-server shared-key-cipher %^%#vS%796FO7%C~pB%CR=q;j}gSCqR-X6+P!.DYI@)%^%# radius-server authentication 192.168.8.249 1812 weight 0 radius-server accounting 192.168.8.249 1813 weight 0 # ip pool huawei bas local gateway 10.11.11.1 255.255.255.0 section 0 10.11.11.2 10.11.11.255 dns-server 192.168.8.252 # user-group huawei # acl number 6000 rule 10 permit ip source user-group huawei destination ip-address 127.0.0.1 0 rule 15 permit ip source ip-address 127.0.0.1 0 destination user-group huawei rule 20 permit ip source user-group huawei destination ip-address 192.168.8.252 0 rule 25 permit ip source ip-address 192.168.8.252 0 destination user-group huawei rule 30 permit ip source user-group huawei destination ip-address 192.168.8.249 0 rule 35 permit ip source ip-address 192.168.8.249 0 destination user-group huawei rule 40 permit ip source user-group huawei destination ip-address 192.168.8.251 0 rule 45 permit ip source ip-address 192.168.8.251 0 destination user-group huawei # acl number 6001 rule 10 permit tcp source user-group huawei destination-port eq www rule 15 permit tcp source user-group huawei destination-port eq 8080 # traffic classifier web_deny operator or if-match acl 6001 precedence 2 # traffic classifier web_permit operator or if-match acl 6000 precedence 1 # traffic behavior web_deny http-redirect # traffic behavior web_permit # traffic policy web share-mode classifier web_permit behavior web_permit classifier web_deny behavior web_deny # aaa # authentication-scheme auth2 # accounting-scheme acct2 # domain default0 ip-pool huawei user-group huawei web-server 192.168.8.251 web-server url http://192.168.8.251 # domain isp2 authentication-scheme auth2 accounting-scheme acct2 radius-server group rd2 # interface GigabitEthernet 0/1/1 undo shutdown ip address 192.168.2.1 255.255.255.0 # interface GigabitEthernet0/1/2 undo shutdown # interface GigabitEthernet0/1/2.1 vlan-type dot1q 1 ip address 192.168.1.1 255.255.255.0 bas # access-type layer3-subscriber default-domain authentication isp2 # web-auth-server enable web-auth-server 192.168.8.251 key cipher %^%#aQL6,Ua<|@sxPQK/1f'4/GBJ6,6)q>$Z^7*,!2yR%^%# # undo web-auth-server source-ip all web-auth-server source-ip 192.168.8.1 # undo web-auth-server source-ipv6 all # traffic-policy web inbound # return