Example for Configuring Defense Against ARP MITM Attacks
Networking Requirements
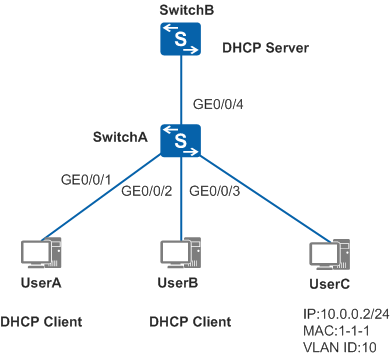
As shown in Figure 1, SwitchA connects to the DHCP server through GE0/0/4, connects to DHCP clients UserA and UserB through GE0/0/1 and GE0/0/2, and connects to UserC configured with a static IP address through GE0/0/3. GE0/0/1, GE0/0/2, GE0/0/3, and GE0/0/4 on SwitchA all belong to VLAN 10. The administrator wants to prevent ARP man-in-the-middle (MITM) attacks and theft on authorized user information, and learn the frequency and scope of ARP MITM attacks.
Configuration Roadmap
- Enable DAI so that SwitchA compares the source IP address, source MAC address, interface number, and VLAN ID of the ARP packet with DHCP snooping binding entries. This prevents ARP MITM attacks.
- Enable the alarm function for the ARP packets discarded by DAI so that SwitchA collects statistics on ARP packets that do not match a DHCP snooping binding entry and generates alarms when the number of discarded ARP packets exceeds the alarm threshold. The administrator learns the frequency and scope of the current ARP MITM attacks based on the alarms and the number of discarded ARP packets.
- Enable DHCP snooping and configure a static binding table to make DAI take effect.
Procedure
- Create a VLAN and add interfaces to the VLAN.
# Create VLAN 10, and add GE0/0/1, GE0/0/2, GE0/0/3, and GE0/0/4 to VLAN 10.
<HUAWEI> system-view [HUAWEI] sysname SwitchA [SwitchA] vlan batch 10 [SwitchA] interface gigabitethernet 0/0/1 [SwitchA-GigabitEthernet0/0/1] port link-type access [SwitchA-GigabitEthernet0/0/1] port default vlan 10 [SwitchA-GigabitEthernet0/0/1] quit [SwitchA] interface gigabitethernet 0/0/2 [SwitchA-GigabitEthernet0/0/2] port link-type access [SwitchA-GigabitEthernet0/0/2] port default vlan 10 [SwitchA-GigabitEthernet0/0/2] quit [SwitchA] interface gigabitethernet 0/0/3 [SwitchA-GigabitEthernet0/0/3] port link-type access [SwitchA-GigabitEthernet0/0/3] port default vlan 10 [SwitchA-GigabitEthernet0/0/3] quit [SwitchA] interface gigabitethernet 0/0/4 [SwitchA-GigabitEthernet0/0/4] port link-type trunk [SwitchA-GigabitEthernet0/0/4] port trunk allow-pass vlan 10 [SwitchA-GigabitEthernet0/0/4] quit
- Enable DAI and the packet discarding alarm function.
# Enable DAI and the packet discarding alarm function on GE0/0/1, GE0/0/2, and GE0/0/3. GE0/0/1 is used as an example. Configurations of GE0/0/2 and GE0/0/3 are similar to the configuration of GE0/0/1, and are not mentioned here.
[SwitchA] interface gigabitethernet 0/0/1 [SwitchA-GigabitEthernet0/0/1] arp anti-attack check user-bind enable [SwitchA-GigabitEthernet0/0/1] arp anti-attack check user-bind alarm enable [SwitchA-GigabitEthernet0/0/1] quit
- Configure DHCP snooping.
# Enable DHCP snooping globally.
[SwitchA] dhcp enable [SwitchA] dhcp snooping enable
# Enable DHCP snooping in VLAN 10.
[SwitchA] vlan 10 [SwitchA-vlan10] dhcp snooping enable [SwitchA-vlan10] quit
# Configure GE0/0/4 as a trusted interface.
[SwitchA] interface gigabitethernet 0/0/4 [SwitchA-GigabitEthernet0/0/4] dhcp snooping trusted [SwitchA-GigabitEthernet0/0/4] quit
# Configure a static binding table.
[SwitchA] user-bind static ip-address 10.0.0.2 mac-address 0001-0001-0001 interface gigabitethernet 0/0/3 vlan 10
- Verify the configuration.
# Run the display arp anti-attack configuration check user-bind interface command to check the DAI configuration on each interface. GE0/0/1 is used as an example.
[SwitchA] display arp anti-attack configuration check user-bind interface gigabitethernet 0/0/1 arp anti-attack check user-bind enable arp anti-attack check user-bind alarm enable
# Run the display arp anti-attack statistics check user-bind interface command to check the number of ARP packets discarded based on DAI. GE0/0/1 is used as an example.
[SwitchA] display arp anti-attack statistics check user-bind interface gigabitethernet 0/0/1 Dropped ARP packet number is 966 Dropped ARP packet number since the latest warning is 605
In the preceding command output, the number of discarded ARP packets on GE0/0/1 is displayed, indicating that the defense against ARP MITM attacks has taken effect.
When you run the display arp anti-attack statistics check user-bind interface command for multiple times on each interface, the administrator can learn the frequency and scope of ARP MITM attacks based on the number of discarded ARP packets.
Configuration File
SwitchA configuration file
# sysname SwitchA # vlan batch 10 # dhcp enable # dhcp snooping enable user-bind static ip-address 10.0.0.2 mac-address 0001-0001-0001 interface GigabitEthernet0/0/3 vlan 10 # vlan 10 dhcp snooping enable # interface GigabitEthernet0/0/1 port link-type access port default vlan 10 arp anti-attack check user-bind enable arp anti-attack check user-bind alarm enable # interface GigabitEthernet0/0/2 port link-type access port default vlan 10 arp anti-attack check user-bind enable arp anti-attack check user-bind alarm enable # interface GigabitEthernet0/0/3 port link-type access port default vlan 10 arp anti-attack check user-bind enable arp anti-attack check user-bind alarm enable # interface GigabitEthernet0/0/4 port link-type trunk port trunk allow-pass vlan 10 dhcp snooping trusted # return