Example for Configuring MAC Address Authentication to Control User Access
MAC Address Authentication Overview
As one of NAC authentication modes, MAC address authentication controls a user's network access rights based on the user's interface and MAC address. The user does not need to install any client software. MAC address authentication ensures security of enterprise intranets.
In MAC address authentication, client software does not need to be installed on user terminals, but MAC addresses must be registered on servers, resulting in complex management. Another two NAC authentication methods have their advantages and disadvantages: 802.1X authentication ensures high security, but it requires that 802.1X client software be installed on user terminals, causing inflexible network deployment. Portal authentication also does not require client software installation and provides flexible deployment, but it has low security.
MAC address authentication is applied to access authentication scenarios of dumb terminals such as printers and fax machines.
Configuration Notes
This configuration example applies to all switches running all versions.
When you run the access-user arp-detect command to configure the IP address and MAC address of the user gateway as the source IP address and source MAC address of user offline detection packets, ensure that the MAC address of the gateway remains unchanged, especially in active/standby switchover scenarios. If the gateway MAC address is changed, ARP entries of terminals will be incorrect on the device, and the terminals cannot communicate with the device.
Networking Requirements
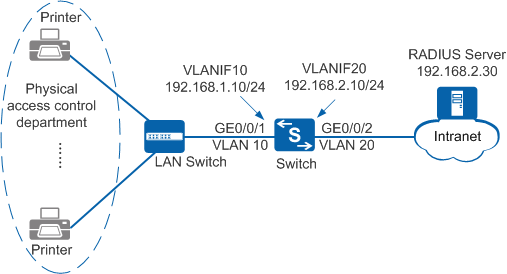
As shown in Figure 1, terminals in a company's physical access control department are connected to the company's internal network through the Switch. Unauthorized access to the internal network can damage the company's service system and cause leakage of key information. Therefore, the administrator requires that the Switch should control users' network access rights to ensure internal network security.
Because dumb terminals (such as printers) in the physical access control department cannot have the authentication client installed, MAC address authentication needs to be configured on the Switch. MAC addresses of terminals are used as user information and sent to the RADIUS server for authentication. When users connect to the network, authentication is not required.
Configuration Roadmap
The configuration roadmap is as follows:
- Configure network interoperation.
- Configure AAA on the Switch to implement identity authentication on access users through the RADIUS server. The configuration includes configuring a RADIUS server template, an AAA scheme, and an authentication domain, and binding the RADIUS server template and AAA scheme to the authentication domain.
- Configure MAC address authentication so that the Switch can control network access rights of the dumb terminals in the physical access control department. The configuration includes:
- Configure a MAC access profile.
- Configure an authentication profile.
- Enable MAC address authentication on an interface.
Procedure
- Create VLANs and configure the VLANs allowed by interfaces so that packets can be forwarded.
# Create VLAN 10 and VLAN 20.
<HUAWEI> system-view [HUAWEI] sysname Switch [Switch] vlan batch 10 20
# Configure GE0/0/1 connecting the Switch to users as an access interface and add the interface to VLAN 10.
[Switch] interface gigabitethernet0/0/1 [Switch-GigabitEthernet0/0/1] port link-type access [Switch-GigabitEthernet0/0/1] port default vlan 10 [Switch-GigabitEthernet0/0/1] quit [Switch] interface vlanif 10 [Switch-Vlanif10] ip address 192.168.1.10 24 [Switch-Vlanif10] quit
# Configure GE0/0/2 connecting the Switch to the RADIUS server as an access interface and add the interface to VLAN 20.
[Switch] interface gigabitethernet0/0/2 [Switch-GigabitEthernet0/0/2] port link-type access [Switch-GigabitEthernet0/0/2] port default vlan 20 [Switch-GigabitEthernet0/0/2] quit [Switch] interface vlanif 20 [Switch-Vlanif20] ip address 192.168.2.10 24 [Switch-Vlanif20] quit
- Configure AAA.
# Create and configure the RADIUS server template rd1.
[Switch] radius-server template rd1 [Switch-radius-rd1] radius-server authentication 192.168.2.30 1812 [Switch-radius-rd1] radius-server shared-key cipher Huawei@2012 [Switch-radius-rd1] quit
# Create the AAA authentication scheme abc and set the authentication mode to RADIUS.
[Switch] aaa [Switch-aaa] authentication-scheme abc [Switch-aaa-authen-abc] authentication-mode radius [Switch-aaa-authen-abc] quit
# Create the authentication domain huawei.com, and bind the AAA authentication scheme abc and RADIUS server template rd1 to the domain.
[Switch-aaa] domain huawei.com [Switch-aaa-domain-huawei.com] authentication-scheme abc [Switch-aaa-domain-huawei.com] radius-server rd1 [Switch-aaa-domain-huawei.com] quit [Switch-aaa] quit
# Check whether a user can pass RADIUS authentication. The test user test and password Huawei2012 have been configured on the RADIUS server.
[Switch] test-aaa test Huawei2012 radius-template rd1 Info: Account test succeeded.
- Configure MAC address authentication.# Set the NAC mode to unified.
[Switch] authentication unified-mode

- By default, the unified mode is used.
- After changing the NAC mode from common to unified, save the configuration and restart the device to make the configuration take effect.
# Configure the MAC access profile m1.

In a MAC access profile, a MAC address without hyphens (-) is used as the user name and password for MAC address authentication. Ensure that the formats of the user name and password for MAC address authentication configured on the RADIUS server are the same as those configured on the access device.
[Switch] mac-access-profile name m1 [Switch-mac-access-profile-m1] quit
# Configure the authentication profile p1, bind the MAC access profile m1 to the authentication profile, specify the domain huawei.com as the forcible authentication domain in the authentication profile, set the user access mode to multi-authen, and set the maximum number of access users to 100.
[Switch] authentication-profile name p1 [Switch-authen-profile-p1] mac-access-profile m1 [Switch-authen-profile-p1] access-domain huawei.com force [Switch-authen-profile-p1] authentication mode multi-authen max-user 100 [Switch-authen-profile-p1] quit
# Bind the authentication profile p1 to GE0/0/1 and enable MAC address authentication on the interface.
[Switch] interface gigabitethernet0/0/1 [Switch-GigabitEthernet0/0/1] authentication-profile p1 [Switch-GigabitEthernet0/0/1] quit
# (Recommended) Configure the source IP address and source MAC address for offline detection packets in a specified VLAN. You are advised to set the user gateway IP address and its corresponding MAC address as the source IP address and source MAC address of offline detection packets.
[Switch] access-user arp-detect vlan 10 ip-address 192.168.1.10 mac-address 2222-1111-1234
- Verify the configuration.
- After a user starts a terminal, the device automatically obtains the user terminal's MAC address as the user name and password for authentication.
- Users can access the network after being authenticated successfully.
- After users go online, you can run the display access-user access-type mac-authen command on the device to view information about online MAC address authentication users.
Configuration Files
Configuration file of the Switch
# sysname Switch # vlan batch 10 20 # authentication-profile name p1 mac-access-profile m1 authentication mode multi-authen max-user 100 access-domain huawei.com force # access-user arp-detect vlan 10 ip-address 192.168.1.10 mac-address 2222-1111-1234 # radius-server template rd1 radius-server shared-key cipher %#%#4*SO-2u,Q.\1C~%[eiB77N/^2wME;6t%6U@qAJ9:%#%# radius-server authentication 192.168.2.30 1812 weight 80 # mac-access-profile name m1 # aaa authentication-scheme abc authentication-mode radius domain huawei.com authentication-scheme abc radius-server rd1 # interface GigabitEthernet0/0/1 port link-type access port default vlan 10 authentication-profile p1 # interface GigabitEthernet0/0/2 port link-type access port default vlan 20 # interface Vlanif10 ip address 192.168.1.10 255.255.255.0 # interface Vlanif20 ip address 192.168.2.10 255.255.255.0 # return