Example for Configuring Built-in Portal Authentication to Control Internal User Access
Networking Requirements
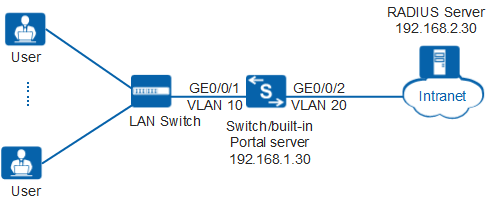
As shown in Figure 1, many users on a company access network through GE0/0/1 of the Switch (used as an access device). After the network operates for a period of time, attacks are detected. The administrator must control network access rights of user terminals to ensure network security. The Switch allows user terminals to access Internet resources only after they are authenticated.
Configuration Roadmap
To control the network access permission of users, the administrator can configure Portal authentication on the Switch after the server with the IP address 192.168.2.30 is configured as the RADIUS server. Due to limited device resources, the administrator uses the built-in Portal server and configures the IP address 192.168.1.30 of a loopback interface of the Switch as the IP address for the built-in Portal server.
The configuration roadmap is as follows (configured on the Switch):
Create and configure a RADIUS server template, an AAA scheme, and an ISP domain; bind the RADIUS server template and the AAA scheme to the ISP domain. The Switch can then exchange information with the RADIUS server.
- Configure built-in Portal authentication so that terminals can connect to the network using Portal authentication.

Before configuring this example, ensure that devices can communicate with each other in the network.
Procedure
- Create VLANs and configure the VLAN allowed by the interface to ensure network communication.
# Create VLAN 10 and VLAN 20.
<HUAWEI> system-view [HUAWEI] sysname Switch [Switch] vlan batch 10 20
# On the Switch, set GE0/0/1 connecting to users as an access interface, and add GE0/0/1 to VLAN 10.
[Switch] interface gigabitethernet 0/0/1 [Switch-GigabitEthernet0/0/1] port link-type access [Switch-GigabitEthernet0/0/1] port default vlan 10 [Switch-GigabitEthernet0/0/1] quit

Configure the interface type and VLANs according to the actual situation. In this example, users are added to VLAN 10.
# On the Switch, set GE0/0/2 connecting to the RADIUS server as an access interface, and add GE0/0/2 to VLAN 20.
[Switch] interface gigabitethernet 0/0/2 [Switch-GigabitEthernet0/0/2] port link-type access [Switch-GigabitEthernet0/0/2] port default vlan 20 [Switch-GigabitEthernet0/0/2] quit
- Configure IP addresses for VLANIF 10 and VLANIF 20.
[HUAWEI] interface vlanif 10 [HUAWEI-Vlanif10] ip address 192.168.3.1 24 [HUAWEI-Vlanif10] quit
[HUAWEI] interface vlanif 20 [HUAWEI-Vlanif20] ip address 192.168.2.1 24 [HUAWEI-Vlanif20] quit
- Create and configure a RADIUS server template, an AAA scheme, and an authentication domain.
# Create and configure RADIUS server template rd1.
[Switch] radius-server template rd1 [Switch-radius-rd1] radius-server authentication 192.168.2.30 1812 [Switch-radius-rd1] radius-server shared-key cipher Huawei@2012 [Switch-radius-rd1] quit
# Create AAA scheme abc and set the authentication mode to RADIUS.
[Switch] aaa [Switch-aaa] authentication-scheme abc [Switch-aaa-authen-abc] authentication-mode radius [Switch-aaa-authen-abc] quit
# Create authentication domain isp1, and bind AAA scheme abc and RADIUS server template rd1 to authentication domain isp1.
[Switch-aaa] domain isp1 [Switch-aaa-domain-isp1] authentication-scheme abc [Switch-aaa-domain-isp1] radius-server rd1 [Switch-aaa-domain-isp1] quit [Switch-aaa] quit
# Configure the default domain isp1 in the system view. When a user enters the user name in the format of user@isp1, the user is authenticated in the authentication domain isp1. If the user name does not carry the domain name or carries a nonexistent domain name, the user is authenticated in the default domain.
[Switch] domain isp1# Test whether a user can be authenticated using RADIUS authentication. A user name test@huawei.com and password Huawei2012 have been configured on the RADIUS server.
[Switch] test-aaa test@huawei.com Huawei2012 radius-template rd1 Info: Account test succeeded. - Configure built-in Portal authentication.
# Switch the NAC mode to common mode.
[Switch] undo authentication unified-mode Warning: Switching the authentication mode will take effect after system restart . Some configurations are invalid after the mode is switched. For the invalid co mmands, see the user manual. Save the configuration file and reboot now? [Y/N] y
- By default, the NAC unified mode is used.
- After the unified mode is switched to common mode, you must save the configuration and restart the device to make each function in the new configuration mode take effect.
# Create a loopback interface and assign an IP address to the loopback interface.
[HUAWEI] interface loopback 6 [HUAWEI-LoopBack6] ip address 192.168.1.30 32 [HUAWEI-LoopBack6] quit
# Configure an IP address for the built-in Portal authentication server.
[HUAWEI] portal local-server ip 192.168.1.30# Configure an SSL policy required for opening the built-in Portal authentication page.
[HUAWEI] ssl policy huawei [HUAWEI-ssl-policy-huawei] certificate load asn1-cert servercert.der key-pair dsa key-file serverkey.der [HUAWEI-ssl-policy-huawei] quit

Before loading a certificate for the SSL policy, ensure that the certificate file and key pair file have been stored on the device; otherwise, the certificate fails to be loaded. In addition, the certificate file and key pair file must be saved in the security subdirectory of the system root directory. If the security subdirectory does not exist, create it.
# Enable built-in Portal authentication.
[HUAWEI] portal local-server https ssl-policy huawei [HUAWEI] interface vlanif 10 [HUAWEI-Vlanif10] portal local-server enable [HUAWEI-Vlanif10] quit
- Verify the configuration.
- Run the display portal local-server commands to check the built-in Portal authentication configuration.
- After starting the browser and entering any network address, the user is redirected to the Portal authentication page. The user then enters the user name and password for authentication.
- If the user name and password are correct, an authentication success message is displayed on the Portal authentication page. The user can access the network.
- After the user goes online, you can run the display access-user command on the device to check the online Portal authentication user information.
Configuration Files
Switch configuration file
# sysname Switch # vlan batch 10 20 undo authentication unified-mode # domain isp1 # portal local-server ip 192.168.1.30 portal local-server https ssl-policy huawei # radius-server template rd1 radius-server shared-key cipher %^%#t67cDelRvAQg;*"4@P/3~q_31Sn{ST\V8'Ci633)%^%# radius-server authentication 192.168.2.30 1812 weight 80 # aaa authentication-scheme abc authentication-mode radius domain isp1 authentication-scheme abc radius-server rd1 # interface Vlanif10 ip address 192.168.3.1 255.255.255.0 portal local-server enable interface Vlanif20 ip address 192.168.2.1 255.255.255.0 # interface GigabitEthernet0/0/1 port link-type access port default vlan 10 # interface GigabitEthernet0/0/2 port link-type access port default vlan 20 # interface LoopBack6 ip address 192.168.1.30 255.255.255.255 # ssl policy huawei certificate load asn1-cert servercert.der key-pair dsa key-file serverkey.der # return