Example for Configuring Terminal Type Identification in 802.1X + RADIUS Authentication
Networking Requirements
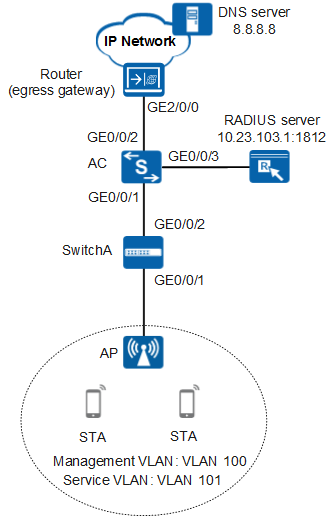
As shown in Figure 1, an enterprise's AC connects to the egress gateway (router) and RADIUS server, and connects to the AP through SwitchA. The WLAN with the SSID wlan-net is available for employees to access network resources. The gateway router also functions as a DHCP server to assign IP addresses on the network segment 10.23.101.0/24 to STAs. The AC controls and manages STAs.
To improve work efficiency, the enterprise allows employees to access the enterprise intranet through the WLAN using their own STAs. Only the STAs of the Huawei type are allowed to access the enterprise intranet to ensure network security.
Configuration Roadmap
- Configure the AP and AC to communicate with upper-layer network devices.
- Configure the AC to assign an IP address to the AP and the router to assign IP addresses to STAs.
- Configure RADIUS authentication parameters.
- Configure an 802.1X access profile to manage 802.1X access control parameters.
- Configure an authentication profile, bind the 802.1X access profile to the authentication profile, and configure a forcible authentication domain for users.
- Configure the terminal type identification function to allow only the STAs of the Huawei type to access the WLAN.
- Configure the AP to go online.
- Configure WLAN service parameters, set the security policy to WPA2-802.1X-AES, and bind a security policy profile and an authentication profile to a VAP profile to control access from STAs.

Ensure that the RADIUS server IP address, port number, and shared key are configured correctly and are the same as those on the RADIUS server. When the AC functions as the EAP relay, ensure that the RADIUS server supports EAP. Otherwise, the AC cannot process 802.1X authentication requests.
When RADIUS authentication is used, the terminal type identified by the device is carried by Huawei proprietary attribute 157 HW-Terminal-Type and sent to the RADIUS server. The RADIUS server must identify this attribute so that it can deliver authorization information based on the user terminal type.
Data plan
Item |
Data |
|---|---|
Management VLAN |
VLAN 100 |
Service VLAN |
VLAN 101 |
AC's source interface |
VLANIF 100: 10.23.100.1/24 |
SwitchA VLAN |
VLAN 100 |
DHCP server |
|
AP's gateway |
VLANIF 100: 10.23.100.1/24 |
STA's gateway |
VLANIF 101: 10.23.101.1/24 |
RADIUS authentication parameters |
|
STA user name and password |
|
802.1X access profile |
|
Authentication profile |
|
AP group |
|
Regulatory domain profile |
|
SSID profile |
|
Security profile |
|
VAP profile |
|
Procedure
- Set the NAC mode to unified on the AC so that users can connect to the network.
<HUAWEI> system-view [HUAWEI] sysname AC [AC] authentication unified-mode

- By default, the unified mode is used.
- After changing the NAC mode from common to unified, save the configuration and restart the device to make the configuration take effect.
- Configure SwitchA and the AC so that the AP and AC can exchange CAPWAP packets.
# On SwitchA, add GE0/0/1 connected to the AP and GE0/0/2 connected to the AC to management VLAN 100.
<HUAWEI> system-view [HUAWEI] sysname SwitchA [SwitchA] vlan batch 100 [SwitchA] interface gigabitethernet 0/0/1 [SwitchA-GigabitEthernet0/0/1] port link-type trunk [SwitchA-GigabitEthernet0/0/1] port trunk pvid vlan 100 [SwitchA-GigabitEthernet0/0/1] port trunk allow-pass vlan 100 [SwitchA-GigabitEthernet0/0/1] port-isolate enable [SwitchA-GigabitEthernet0/0/1] quit [SwitchA] interface gigabitethernet 0/0/2 [SwitchA-GigabitEthernet0/0/2] port link-type trunk [SwitchA-GigabitEthernet0/0/2] port trunk allow-pass vlan 100 [SwitchA-GigabitEthernet0/0/2] quit
# On the AC, add GE0/0/1 connected to SwitchA to VLAN 100.
[AC] vlan batch 100 [AC] interface gigabitethernet 0/0/1 [AC-GigabitEthernet0/0/1] port link-type trunk [AC-GigabitEthernet0/0/1] port trunk allow-pass vlan 100 [AC-GigabitEthernet0/0/1] quit
- Configure the AC to communicate with upper-layer network devices.
# Configure VLANIF 101 (of the service VLAN), VLANIF 102, and VLANIF 103.
[AC] vlan batch 101 102 103 [AC] interface vlanif 101 [AC-Vlanif101] ip address 10.23.101.1 24 [AC-Vlanif101] quit [AC] interface vlanif 102 [AC-Vlanif102] ip address 10.23.102.2 24 [AC-Vlanif102] quit [AC] interface vlanif 103 [AC-Vlanif103] ip address 10.23.103.2 24 [AC-Vlanif103] quit
# On the AC, add GE0/0/2 connected to the router to VLAN 102.
[AC] interface gigabitethernet 0/0/2 [AC-GigabitEthernet0/0/2] port link-type trunk [AC-GigabitEthernet0/0/2] port trunk allow-pass vlan 102 [AC-GigabitEthernet0/0/2] quit
# On the AC, add GE0/0/3 connected to the RADIUS server to VLAN 103.
[AC] interface gigabitethernet 0/0/3 [AC-GigabitEthernet0/0/3] port link-type trunk [AC-GigabitEthernet0/0/3] port trunk pvid vlan 103 [AC-GigabitEthernet0/0/3] port trunk allow-pass vlan 103 [AC-GigabitEthernet0/0/3] quit
# Configure the default route on the AC.
[AC] ip route-static 0.0.0.0 0.0.0.0 10.23.102.1
- Configure the AC to assign an IP address to the AP and the router to assign IP addresses to STAs.
# Configure the AC to assign IP addresses to APs from an interface address pool.
[AC] dhcp enable [AC] interface vlanif 100 [AC-Vlanif100] ip address 10.23.100.1 24 [AC-Vlanif100] dhcp select interface [AC-Vlanif100] quit
# Configure the AC as a DHCP relay agent and specify the DHCP server IP address on the DHCP relay agent.
[AC] interface vlanif 101 [AC-Vlanif101] dhcp select relay [AC-Vlanif101] dhcp relay server-ip 10.23.102.1 [AC-Vlanif101] quit
# Configure the router as a DHCP server to assign IP addresses to STAs from the global address pool. The egress gateway address for DHCP clients is 10.23.101.1 and the network segment for the global address pool is 10.23.101.0/24.
<Huawei> system-view [Huawei] sysname Router [Router] dhcp enable [Router] ip pool sta [Router-ip-pool-sta] gateway-list 10.23.101.1 [Router-ip-pool-sta] dns-list 8.8.8.8 [Router-ip-pool-sta] network 10.23.101.0 mask 24 [Router-ip-pool-sta] quit [Router] vlan batch 102 [Router] interface vlanif 102 [Router-Vlanif102] ip address 10.23.102.1 24 [Router-Vlanif102] dhcp select global [Router-Vlanif102] quit [Router] interface gigabitethernet 2/0/0 [Router-GigabitEthernet2/0/0] port link-type trunk [Router-GigabitEthernet2/0/0] port trunk allow-pass vlan 102 [Router-GigabitEthernet2/0/0] quit [Router] ip route-static 10.23.101.0 24 10.23.102.2
- Configure RADIUS authentication parameters.
# Create a RADIUS server template.
[AC] radius-server template radius_huawei [AC-radius-radius_huawei] radius-server authentication 10.23.103.1 1812 [AC-radius-radius_huawei] radius-server shared-key cipher huawei@123 [AC-radius-radius_huawei] quit
# Create a RADIUS authentication scheme.
[AC] aaa [AC-aaa] authentication-scheme radius_huawei [AC-aaa-authen-radius_huawei] authentication-mode radius [AC-aaa-authen-radius_huawei] quit
# Create an AAA domain and configure the RADIUS server template and authentication scheme for the domain.
[AC-aaa] domain huawei.com [AC-aaa-domain-huawei.com] radius-server radius_huawei [AC-aaa-domain-huawei.com] authentication-scheme radius_huawei [AC-aaa-domain-huawei.com] quit [AC-aaa] quit

After the domain name huawei.com is configured, the domain name is added to the user name.
# Check whether a user can pass RADIUS authentication. (The test user test@huawei.com and password 123456 have been configured on the RADIUS server.)
[AC] test-aaa test@huawei.com 123456 radius-template radius_huawei Info: Account test succeeded.
- Configure an 802.1X access profile to manage 802.1X access control parameters.
# Create the 802.1X access profile wlan-dot1x.
[AC] dot1x-access-profile name wlan-dot1x
# Configure EAP relay authentication.
[AC-dot1x-access-profile-wlan-dot1x] dot1x authentication-method eap [AC-dot1x-access-profile-wlan-dot1x] quit
- Create the authentication profile wlan-authentication, bind the 802.1X access profile to the authentication profile, and configure a forcible authentication domain for users.
[AC] authentication-profile name wlan-authentication [AC-authen-profile-wlan-authentication] dot1x-access-profile wlan-dot1x [AC-authen-profile-wlan-authentication] access-domain huawei.com dot1x force [AC-authen-profile-wlan-authentication] quit
- Configure the terminal type identification function.
# Enable the terminal type awareness function.
[AC] device-sensor dhcp option 12 55 60
# Enable the UA function.
[AC] http parse user-agent enable
# Create the terminal type identification profile huawei.
[AC] device-profile profile-name huawei [AC-device-profile-huawei] device-type huawei [AC-device-profile-huawei] rule 0 dhcp-option 12 sub-match ascii android-9f09b5dc88a64c37 [AC-device-profile-huawei] rule 1 dhcp-option 55 sub-match ascii \001!\003\006\017\0343:; [AC-device-profile-huawei] rule 2 dhcp-option 60 sub-match ascii dhcpcd-5.2.10 [AC-device-profile-huawei] rule 3 mac fcff-ffff-ffff mask 8 [AC-device-profile-huawei] rule 4 user-agent sub-match Mozille/5.0 (Linux; U; Android 4.1.2; zh-CN; ZTE U956 Build/JZ054K) AppleWebKit/534.31 (KHTNL, like Gecko) UCBrowser/8.8.3.276 U3/0.8.8 Moblie Sofari/534.31 [AC-device-profile-huawei] if-match rule 0 or rule 1 or rule 2 or rule 3 or rule 4 [AC-device-profile-huawei] enable [AC-device-profile-huawei] quit
- Configure the AP to go online.
# Create an AP group to which the APs with the same configuration can be added.
[AC] wlan [AC-wlan-view] ap-group name ap-group1 [AC-wlan-ap-group-ap-group1] quit
# Create a regulatory domain profile, configure the AC country code in the profile, and apply the profile to the AP group.
[AC-wlan-view] regulatory-domain-profile name domain1 [AC-wlan-regulatory-domain-prof-domain1] country-code cn [AC-wlan-regulatory-domain-prof-domain1] quit [AC-wlan-view] ap-group name ap-group1 [AC-wlan-ap-group-ap-group1] regulatory-domain-profile domain1 Warning: Modifying the country code will clear channel, power and antenna gain configurations of the radio and reset the AP. Continue?[Y/N]:y [AC-wlan-ap-group-ap-group1] quit [AC-wlan-view] quit# Configure the AC's source interface.
[AC] capwap source interface vlanif 100
# Import the AP offline on the AC and add the AP to the AP group ap-group1. In this example, the AP's MAC address is 60de-4476-e360. Configure a name for the AP based on the AP's deployment location, so that you can know where the AP is located. For example, if the AP with MAC address 60de-4476-e360 is deployed in area 1, name the AP area_1.
[AC] wlan [AC-wlan-view] ap auth-mode mac-auth [AC-wlan-view] ap-id 0 ap-mac 60de-4476-e360 [AC-wlan-ap-0] ap-name area_1 [AC-wlan-ap-0] ap-group ap-group1 Warning: This operation may cause AP reset. If the country code changes, it will clear channel, power and antenna gain configuration s of the radio, Whether to continue? [Y/N]:y [AC-wlan-ap-0] quit# After the AP is powered on, run the display ap all command to check the AP state. If the State field displays nor, the AP has gone online.
[AC-wlan-view] display ap all Total AP information: nor : normal [1] -------------------------------------------------------------------------------- ID MAC Name Group IP Type State STA Uptime -------------------------------------------------------------------------------- 0 60de-4476-e360 area_1 ap-group1 10.23.100.254 AP6010DN-AGN nor 0 10S -------------------------------------------------------------------------------- Total: 1 - Configure WLAN service parameters.
# Create the security profile wlan-security and set the security policy in the profile.
[AC-wlan-view] security-profile name wlan-security [AC-wlan-sec-prof-wlan-security] security wpa2 dot1x aes [AC-wlan-sec-prof-wlan-security] quit
# Create the SSID profile wlan-ssid and set the SSID name to wlan-net.
[AC-wlan-view] ssid-profile name wlan-ssid [AC-wlan-ssid-prof-wlan-ssid] ssid wlan-net Warning: This action may cause service interruption. Continue?[Y/N]y [AC-wlan-ssid-prof-wlan-ssid] quit# Create the VAP profile wlan-vap, configure the data forwarding mode and service VLANs, and apply the security profile, authentication profile, and SSID profile to the VAP profile.
[AC-wlan-view] vap-profile name wlan-vap [AC-wlan-vap-prof-wlan-vap] forward-mode tunnel Warning: This action may cause service interruption. Continue?[Y/N]y [AC-wlan-vap-prof-wlan-vap] service-vlan vlan-id 101 [AC-wlan-vap-prof-wlan-vap] security-profile wlan-security [AC-wlan-vap-prof-wlan-vap] authentication-profile wlan-authentication [AC-wlan-vap-prof-wlan-vap] ssid-profile wlan-ssid [AC-wlan-vap-prof-wlan-vap] quit# Bind the VAP profile wlan-vap to the AP group and apply the profile to radio 0 and radio 1 of the AP.
[AC-wlan-view] ap-group name ap-group1 [AC-wlan-ap-group-ap-group1] vap-profile wlan-vap wlan 1 radio all [AC-wlan-ap-group-ap-group1] quit
- Verify the configuration.
- The WLAN with the SSID wlan-net is available for STAs after the configuration is complete.
- The STAs obtain IP addresses when they successfully associate with the WLAN.
- If an STA of the Huawei type has the CHAP-support client software installed, the STA can be successfully authenticated and access the Internet after the correct user name and password are entered. If an STA of a non-Huawei type has the CHAP-support client software installed, the STA cannot be authenticated even if the correct user name and password are entered.
Configuration Files
Access switch configuration file
# sysname SwitchA # vlan batch 100 # interface GigabitEthernet0/0/1 port link-type trunk port trunk pvid vlan 100 port trunk allow-pass vlan 100 port-isolate enable group 1 # interface GigabitEthernet0/0/2 port link-type trunk port trunk allow-pass vlan 100 # return
Router configuration file
# sysname Router # vlan batch 102 # dhcp enable # ip pool sta gateway-list 10.23.101.1 network 10.23.101.0 mask 255.255.255.0 dns-list 8.8.8.8 # interface Vlanif102 ip address 10.23.102.1 255.255.255.0 dhcp select global # interface GigabitEthernet2/0/0 port link-type trunk port trunk allow-pass vlan 102 # ip route-static 10.23.101.0 255.255.255.0 10.23.102.2 # return
AC configuration file
# sysname AC # vlan batch 100 to 103 # authentication-profile name wlan-authentication dot1x-access-profile wlan-dot1x access-domain huawei.com dot1x force # device-sensor dhcp option 12 55 60 # dhcp enable # radius-server template radius_huawei radius-server shared-key cipher %^%#*7d1;XNof/|Q0:DsP!,W51DIYPx}`AARBdJ'0B^$%^%# radius-server authentication 10.23.103.1 1812 weight 80 # aaa authentication-scheme radius_huawei authentication-mode radius domain huawei.com authentication-scheme radius_huawei radius-server radius_huawei # interface Vlanif100 ip address 10.23.100.1 255.255.255.0 dhcp select interface # interface Vlanif101 ip address 10.23.101.1 255.255.255.0 dhcp select relay dhcp relay server-ip 10.23.102.1 # interface Vlanif102 ip address 10.23.102.2 255.255.255.0 # interface Vlanif103 ip address 10.23.103.2 255.255.255.0 # interface GigabitEthernet0/0/1 port link-type trunk port trunk allow-pass vlan 100 # interface GigabitEthernet0/0/2 port link-type trunk port trunk allow-pass vlan 102 # interface GigabitEthernet0/0/3 port link-type trunk port trunk pvid vlan 103 port trunk allow-pass vlan 103 # ip route-static 0.0.0.0 0.0.0.0 10.23.102.1 # http parse user-agent enable # capwap source interface vlanif100 # wlan security-profile name wlan-security security wpa2 dot1x aes ssid-profile name wlan-ssid ssid wlan-net vap-profile name wlan-vap forward-mode tunnel service-vlan vlan-id 101 ssid-profile wlan-ssid security-profile wlan-security authentication-profile wlan-authentication regulatory-domain-profile name domain1 ap-group name ap-group1 regulatory-domain-profile domain1 radio 0 vap-profile wlan-vap wlan 1 radio 1 vap-profile wlan-vap wlan 1 ap-id 0 ap-mac 60de-4476-e360 ap-name area_1 ap-group ap-group1 # device-profile profile-name huawei device-type huawei enable rule 0 dhcp-option 12 sub-match ascii android-9f09b5dc88a64c37 rule 1 dhcp-option 55 sub-match ascii \001!\003\006\017\0343:; rule 2 dhcp-option 60 sub-match ascii dhcpcd-5.2.10 rule 3 mac fcff-ffff-ffff mask 8 rule 4 user-agent sub-match Mozille/5.0 (Linux; U; Android 4.1.2; zh-CN; ZTE U956 Build/JZ054K) AppleWebKit/534.31 (KHTNL, like Gec ko) UCBrowser/8.8.3.276 U3/0.8.8 Moblie Sofari/534.31 if-match rule 0 or rule 1 or rule 2 or rule 3 or rule 4 # dot1x-access-profile name wlan-dot1x # return