Example for Configuring 802.1X Authentication (Authentication Point on the Access Switch)
Networking Requirements
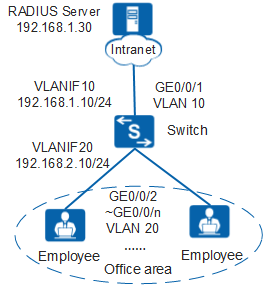
In Figure 1, terminals in a company's offices are connected to the company's intranet through the switch. GE0/0/2 to GE0/0/n on the switch are directly connected to terminals in offices. GE0/0/1 on the switch is connected to the RADIUS server through the intranet.
To meet the company's high security requirements, configure 802.1X authentication, use the RADIUS server to authenticate terminals in offices, and deploy authentication points on GE0/0/2 to GE0/0/n of the switch.
Procedure
- Configure AAA.
# Create and configure the RADIUS server template rd1.
[Switch] radius-server template rd1 [Switch-radius-rd1] radius-server authentication 192.168.1.30 1812 [Switch-radius-rd1] radius-server shared-key cipher Huawei@2012 [Switch-radius-rd1] quit
# Create the AAA authentication scheme abc and set the authentication mode to RADIUS.
[Switch] aaa [Switch-aaa] authentication-scheme abc [Switch-aaa-authen-abc] authentication-mode radius [Switch-aaa-authen-abc] quit
# Create the authentication domain huawei.com, and bind the AAA authentication scheme abc and RADIUS server template rd1 to the domain.
[Switch-aaa] domain huawei.com [Switch-aaa-domain-huawei.com] authentication-scheme abc [Switch-aaa-domain-huawei.com] radius-server rd1 [Switch-aaa-domain-huawei.com] quit [Switch-aaa] quit
# Check whether a user can pass RADIUS authentication. (The test user test and password Huawei2012 have been configured on the RADIUS server.)
[Switch] test-aaa test Huawei2012 radius-template rd1 Info: Account test succeeded.
- Configure 802.1X authentication.# Set the NAC mode to unified.

By default, the unified mode is enabled. After the NAC mode is changed, the device automatically restarts.
[Switch] authentication unified-mode
# Configure the 802.1X access profile d1.[Switch] dot1x-access-profile name d1 [Switch-dot1x-access-profile-d1] dot1x authentication-method eap [Switch-dot1x-access-profile-d1] dot1x timer client-timeout 30 [Switch-dot1x-access-profile-d1] quit

By default, an 802.1X access profile uses the EAP authentication mode. Ensure that the RADIUS server supports EAP; otherwise, the server cannot process 802.1X authentication request packets.
# Configure the authentication profile p1, bind the 802.1X access profile d1 to the authentication profile, specify the domain huawei.com as the forcible authentication domain in the authentication profile.
[Switch] authentication-profile name p1 [Switch-authen-profile-p1] dot1x-access-profile d1 [Switch-authen-profile-p1] access-domain huawei.com force [Switch-authen-profile-p1] quit
# Bind the authentication profile p1 to GE0/0/2 to GE0/0/n and enable 802.1X authentication. The following uses the configuration of GE0/0/2 as an example. The configurations of other interfaces are similar to the configuration of GE0/0/2, and are not mentioned here.
[Switch] interface gigabitethernet 0/0/2 [Switch-GigabitEthernet0/0/2] authentication-profile p1 [Switch-GigabitEthernet0/0/2] quit
- Verify the configuration.
- A user starts the 802.1X client on a terminal, and enters the user name and password for authentication.
- If the user name and password are correct, an authentication success message is displayed on the client page. The user can access the network.
- After users go online, you can run the display access-user access-type dot1x command on the switch to view information about online 802.1X authentication users.