Defense Against ARP Flood Attacks
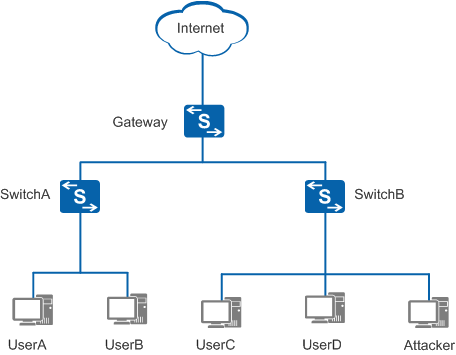
As shown in Figure 1, user hosts connect to the gateway through SwitchA and SwitchB. If a large number of ARP packets are broadcast on the network, the gateway cannot process other services due to CPU overload. Processing too many ARP packets will occupy considerable bandwidth, thus leading to network congestion and affecting network communication.
To avoid the preceding problems, deploy ARP flood defense functions on the gateway, including rate limiting on ARP packets, rate limiting on ARP Miss messages, strict ARP learning, and ARP entry limiting.
After rate limiting on ARP packets is deployed, the gateway collects statistics on received ARP packets. If the number of ARP packets received within a specified period exceeds the threshold (the maximum number of ARP packets), the gateway discards the excess ARP packets to prevent CPU overload.
After rate limiting on ARP Miss messages is deployed, the gateway collects statistics on ARP Miss messages. If the number of ARP Miss messages generated within a specified period exceeds the threshold (the maximum number of ARP Miss messages), the gateway discards the IP packets triggering the excess ARP Miss messages. This prevents CPU overload when the gateway processes a large number of IP packets with unresolvable IP addresses.
After strict ARP learning is deployed, the gateway learns only the ARP Reply packets in response to the ARP Request packets that it has sent. This action prevents ARP entries on the gateway from being exhausted when the gateway processes many ARP packets.
After ARP entry limiting is deployed, the gateway limits the number of ARP entries dynamically learned by each interface. When the number of the ARP entries dynamically learned by an interface reaches the maximum number, no more dynamic entries can be added. This prevents ARP entries from being exhausted when a host connected to the interface attacks the gateway.