Defense Against ARP Spoofing Attacks
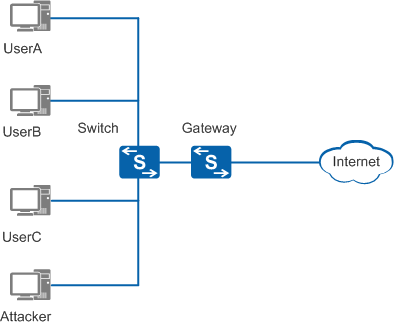
As shown in Figure 1, UserA, UserB, and UserC use Switch to connect to the gateway to access the Internet.
Generally, when UserA, UserB, and UserC go online and exchange ARP packets, ARP entries are created on UserA, UserB, UserC, and the gateway. At the same time, an attacker can send bogus ARP packets to UserA, UserB, UserC, or the gateway in the broadcast domain to modify ARP entries, intercept information, and interrupt communication.
To avoid the preceding problems, deploy ARP spoofing defense functions on the gateway, including ARP entry fixing, strict ARP learning, and gratuitous ARP packet sending. You can deploy DAI on the access device for DHCP users.
After ARP entry fixing is deployed and the gateway learns an ARP entry for the first time, the gateway does not update the entry, updates only part of the entry, or sends a unicast ARP Request packet to check the validity of the ARP packet for updating the entry. This function prevents ARP entries from being modified by bogus ARP packets.
After strict ARP learning is deployed, the gateway learns only the ARP Reply packets in response to the ARP Request packets that it has sent. This prevents ARP entries from being modified by bogus ARP packets.
After gratuitous ARP packet sending is deployed, the gateway periodically sends ARP Request packets with its IP address as the destination IP address to update the gateway MAC address in ARP entries. This function ensures that packets of authorized users are forwarded to the gateway and prevents hackers from intercepting these packets.
The DAI function allows the switch to compare the source IP address, source MAC address, interface number, and VLAN ID of an ARP packet with binding entries. If the ARP packet matches a binding entry, the device considers the ARP packet valid and allows the packet to pass through. If the ARP packet does not match a binding entry, the device considers the ARP packet invalid and discards the packet. This function prevents MITM attacks.