Example for Configuring Portal Authentication on the Wireless Side (on a Layer 2 Network)
Portal Authentication on the Wireless Side Overview
Portal authentication is also called web authentication. Generally, Portal authentication websites are also called Portal websites. When users go online, they must be authenticated on Portal websites. The users can use network resources only after they pass the authentication.
A user can access a known Portal authentication website and enter a user name and password for authentication. This mode is called active authentication. If a user attempts to access other external networks through HTTP, the device forcibly redirects the user to the Portal authentication website for Portal authentication. This mode is called forcible authentication.
Configuration Notes
For details about common WLAN configuration notes, see General Precautions for WLAN. For more deployment and configuration suggestions, see Wireless Network Deployment and Configuration Suggestions.
Configure a proper RADIUS packet retransmission timeout interval.
For a large-scale or busy network, configure the shortest retransmission timeout interval for RADIUS request packets. When a long retransmission timeout interval is set, retransmission occupies system resources. A short retransmission timeout interval can improve the AC's packet processing capability.
The default retransmission timeout interval for wireless users is 5 seconds, which is suitable for most wireless user authentication scenarios. When IP addresses of more than eight authentication servers are configured in a RADIUS server template, or 802.1X authentication is used, it is recommended that the retransmission timeout interval be set to 1 second to improve network processing efficiency.
From V200R011C10, WLAN configurations are automatically delivered, without the need of running the commit all command.
- In this example, Portal authentication is used. To ensure network security, configure an appropriate security policy according to service requirements.
In direct forwarding mode, configure port isolation on the interface directly connected to APs. If port isolation is not configured, many broadcast packets will be transmitted in the VLANs or WLAN users on different APs can directly communicate at Layer 2.
- Configure the management VLAN and service VLAN:
- In tunnel forwarding mode, service packets are encapsulated in a CAPWAP tunnel and forwarded to the AC. The AC then forwards the packets to the upper-layer network. Service packets and management packets can be forwarded normally only if the network between the AC and APs is added to the management VLAN and the network between the AC and upper-layer network is added to the service VLAN.
- In direct forwarding mode, service packets are not encapsulated into a CAPWAP tunnel, but are directly forwarded to the upper-layer network. Service packets and management packets can be forwarded normally only if the network between APs and upper-layer network is added to the service VLAN and the network between the AC and APs is added to the management VLAN.
- No ACK mechanism is provided for multicast packet transmission on air interfaces. In addition, wireless links are unstable. To ensure stable transmission of multicast packets, they are usually sent at low rates. If a large number of such multicast packets are sent from the network side, the air interfaces may be congested. You are advised to configure multicast packet suppression to reduce impact of a large number of low-rate multicast packets on the wireless network. Exercise caution when configuring the rate limit; otherwise, the multicast services may be affected.
- In direct forwarding mode, you are advised to configure multicast packet suppression on switch interfaces connected to APs.
- In tunnel forwarding mode, you are advised to configure multicast packet suppression in traffic profiles of the AC.
Networking Requirements
Users in the guest area of a company want to access the company's intranet through an AP. The company needs to deploy an identity authentication system for access control of users who attempt to connect to the network, preventing unauthorized access.
Because visitors move frequently, Portal authentication is configured and the RADIUS server is used to authenticate users.
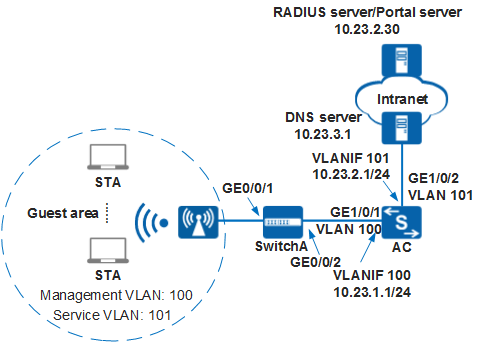
Data Plan
Item |
Data |
|---|---|
DHCP server |
The AC functions as a DHCP server to assign IP addresses to the AP and STAs. |
IP address pool for APs |
10.23.1.2 to 10.23.1.254/24 |
IP address pool for STAs |
10.23.2.2 to 10.23.2.254/24 |
IP address of the AC's source interface |
VLANIF100: 10.23.1.1/24 |
RADIUS authentication parameters |
Name of the RADIUS authentication scheme: abc Name of a RADIUS server template: rd1
AAA domain: huawei.com |
Portal server template |
|
Portal access profile |
|
Authentication-free rule template |
|
Authentication profile |
|
AP group |
|
Regulatory domain profile |
|
SSID profile |
|
Security profile |
|
VAP profile |
|
Configuration Roadmap
- Configure basic WLAN services so that the AC can communicate with upstream and downstream network devices, and the AP can go online.
- Configure AAA on the AC to implement identity authentication on access users through the RADIUS server. The configuration includes configuring a RADIUS server template, an AAA scheme, and an authentication domain, and binding the RADIUS server template and AAA scheme to the authentication domain.
- Configure Portal authentication. The configuration includes configuring a Portal server template, a Portal access profile, an authentication-free rule profile, and an authentication profile, and binding the authentication profile to an interface.
- Configure WLAN service parameters, and bind a security policy profile and an authentication profile to a VAP profile to control access from STAs.
Procedure
- Set the NAC mode to unified mode on the AC (default setting). Configure SwitchA and the AC to allow the AP and AC to transmit CAPWAP packets.
# On SwitchA, add GE0/0/1 connected to the AP and GE0/0/2 connected to the AC to the management VLAN 100.
<HUAWEI> system-view [HUAWEI] sysname SwitchA [SwitchA] vlan batch 100 [SwitchA] interface gigabitethernet 0/0/1 [SwitchA-GigabitEthernet0/0/1] port link-type trunk [SwitchA-GigabitEthernet0/0/1] port trunk pvid vlan 100 [SwitchA-GigabitEthernet0/0/1] port trunk allow-pass vlan 100 [SwitchA-GigabitEthernet0/0/1] undo port trunk allow-pass vlan 1 [SwitchA-GigabitEthernet0/0/1] stp edged-port enable [SwitchA-GigabitEthernet0/0/1] port-isolate enable [SwitchA-GigabitEthernet0/0/1] quit [SwitchA] interface gigabitethernet 0/0/2 [SwitchA-GigabitEthernet0/0/2] port link-type trunk [SwitchA-GigabitEthernet0/0/2] port trunk allow-pass vlan 100 [SwitchA-GigabitEthernet0/0/2] undo port trunk allow-pass vlan 1 [SwitchA-GigabitEthernet0/0/2] quit
# Add GE1/0/1 of the AC connected to SwitchA to VLAN 100.
<HUAWEI> system-view [HUAWEI] sysname AC [AC] vlan batch 100 101 [AC] interface gigabitethernet 1/0/1 [AC-GigabitEthernet1/0/1] port link-type trunk [AC-GigabitEthernet1/0/1] port trunk allow-pass vlan 100 [AC-GigabitEthernet1/0/1] undo port trunk allow-pass vlan 1 [AC-GigabitEthernet1/0/1] quit
- Configure the AC to communicate with upper-layer network devices.

Configure the AC's upstream interfaces to transparently transmit service VLAN packets and communicate with upstream network devices.
# Add GE1/0/2 of the AC connected to an upper-layer device to VLAN 101 (service VLAN).
[AC] interface gigabitethernet 1/0/2 [AC-GigabitEthernet1/0/2] port link-type trunk [AC-GigabitEthernet1/0/2] port trunk allow-pass vlan 101 [AC-GigabitEthernet1/0/2] undo port trunk allow-pass vlan 1 [AC-GigabitEthernet1/0/2] quit
- Configure the AC as a DHCP server to assign IP addresses to the AP and STAs.
# Configure the AC as the DHCP server to assign an IP address to the AP from the IP address pool on VLANIF 100, and assign IP addresses to STAs from the IP address pool on VLANIF 101.
 Configure the DNS server as required. The common methods are as follows:
Configure the DNS server as required. The common methods are as follows:- In interface address pool scenarios, run the dhcp server dns-list ip-address &<1-8> command in the VLANIF interface view.
- In global address pool scenarios, run the dns-list ip-address &<1-8> command in the IP address pool view.
[AC] dhcp enable //Enable the DHCP function. [AC] interface vlanif 100 [AC-Vlanif100] ip address 10.23.1.1 24 [AC-Vlanif100] dhcp select interface //Configure an interface-based address pool. [AC-Vlanif100] quit [AC] interface vlanif 101 [AC-Vlanif101] ip address 10.23.2.1 24 [AC-Vlanif101] dhcp select interface [AC-Vlanif101] quit
- Configure the AP to go online.
# Create an AP group.
[AC] wlan [AC-wlan-view] ap-group name ap-group1 [AC-wlan-ap-group-ap-group1] quit
# Create a regulatory domain profile, configure the AC country code in the profile, and apply the profile to the AP group.
[AC-wlan-view] regulatory-domain-profile name domain1 [AC-wlan-regulate-domain-domain1] country-code cn [AC-wlan-regulate-domain-domain1] quit [AC-wlan-view] ap-group name ap-group1 [AC-wlan-ap-group-ap-group1] regulatory-domain-profile domain1 Warning: Modifying the country code will clear channel, power and antenna gain configurations of the radio and reset the AP. Continue?[Y/N]:y [AC-wlan-ap-group-ap-group1] quit [AC-wlan-view] quit
# Configure the AC's source interface.
[AC] capwap source interface vlanif 100
# Import the AP offline on the AC and add the AP to AP group ap-group1. In this example, the AP's MAC address is 60de-4476-e360. Configure a name for the AP based on the AP's deployment location, so that you can know where the AP is located. For example, if the AP with MAC address 60de-4476-e360 is deployed in area 1, name the AP area_1.
The default AP authentication mode is MAC address authentication. If the default settings are retained, you do not need to run the ap auth-mode mac-auth command.
In this example, the AP5030DN is used and has two radios: radio 0 and radio 1. Radio 0 of the AP5030DN works on the 2.4 GHz frequency band and radio 1 works on the 5 GHz frequency band.
[AC] wlan [AC-wlan-view] ap auth-mode mac-auth [AC-wlan-view] ap-id 0 ap-mac 60de-4476-e360 [AC-wlan-ap-0] ap-name area_1 Warning: This operation may cause AP reset. Continue? [Y/N]:y [AC-wlan-ap-0] ap-group ap-group1 Warning: This operation may cause AP reset. If the country code changes, it will clear channel, power and antenna gain configuration s of the radio, Whether to continue? [Y/N]:y [AC-wlan-ap-0] quit [AC-wlan-view] quit# Power on the AP and run the display ap all command to check the AP state. If the State field is nor, the AP has gone online.
[AC] display ap all Total AP information: nor : normal [1] ------------------------------------------------------------------------------------- ID MAC Name Group IP Type State STA Uptime ------------------------------------------------------------------------------------- 0 60de-4476-e360 area_1 ap-group1 10.23.1.254 AP6010DN-AGN nor 0 10S ------------------------------------------------------------------------------------- Total: 1
- Configure AAA.
# Create and configure the RADIUS server template rd1.
[AC] radius-server template rd1 [AC-radius-rd1] radius-server authentication 10.23.2.30 1812 [AC-radius-rd1] radius-server shared-key cipher Huawei@123 [AC-radius-rd1] quit
# Create the AAA authentication scheme abc and set the authentication mode to RADIUS.
[AC] aaa [AC-aaa] authentication-scheme abc [AC-aaa-authen-abc] authentication-mode radius [AC-aaa-authen-abc] quit
# Create the authentication domain huawei.com, and bind the AAA authentication scheme abc and RADIUS server template rd1 to the domain.
[AC-aaa] domain huawei.com [AC-aaa-domain-huawei.com] authentication-scheme abc [AC-aaa-domain-huawei.com] radius-server rd1 [AC-aaa-domain-huawei.com] quit [AC-aaa] quit
# Check whether a user can pass RADIUS authentication. (The test user test and password Huawei@123 have been configured on the RADIUS server.)
[AC] test-aaa test Huawei@123 radius-template rd1 Info: Account test succeed.
- Configure Portal authentication.# Configure the Portal server template abc.
[AC] web-auth-server abc [AC-web-auth-server-abc] server-ip 10.23.2.30 [AC-web-auth-server-abc] port 50200 [AC-web-auth-server-abc] url http://10.23.2.30:8080/webagent [AC-web-auth-server-abc] shared-key cipher Huawei@123 [AC-web-auth-server-abc] quit
# Configure the Portal access profile web1.[AC] portal-access-profile name web1 [AC-portal-acces-profile-web1] web-auth-server abc direct [AC-portal-acces-profile-web1] quit
# Configure the authentication-free rule profile default_free_rule.[AC] free-rule-template name default_free_rule [AC-free-rule-default_free_rule] free-rule 1 destination ip 10.23.3.1 mask 32 [AC-free-rule-default_free_rule] quit
# Configure the authentication profile p1, bind the Portal access profile web1, and authentication-free rule profile default_free_rule to the authentication profile, specify the domain huawei.com as the forcible authentication domain in the authentication profile, set the user access mode to multi-authen, and set the maximum number of access users to 100.
[AC] authentication-profile name p1 [AC-authen-profile-p1] portal-access-profile web1 [AC-authen-profile-p1] free-rule-template default_free_rule [AC-authen-profile-p1] access-domain huawei.com force [AC-authen-profile-p1] authentication mode multi-authen max-user 100 [AC-authen-profile-p1] quit
- Configure WLAN service parameters.
# Create security profile wlan-security and set the security policy in the profile. By default, the security policy is set to open system.
[AC] wlan [AC-wlan-view] security-profile name wlan-security [AC-wlan-sec-prof-wlan-security] quit
# Create SSID profile wlan-ssid and set the SSID name to wlan-net.
[AC-wlan-view] ssid-profile name wlan-ssid [AC-wlan-ssid-prof-wlan-ssid] ssid wlan-net [AC-wlan-ssid-prof-wlan-ssid] quit
# Create the VAP profile wlan-vap, configure the data forwarding mode and service VLANs, and bind the security profile, authentication profile, and SSID profile to the VAP profile.
[AC-wlan-view] vap-profile name wlan-vap [AC-wlan-vap-prof-wlan-vap] forward-mode tunnel [AC-wlan-vap-prof-wlan-vap] service-vlan vlan-id 101 [AC-wlan-vap-prof-wlan-vap] security-profile wlan-security [AC-wlan-vap-prof-wlan-vap] ssid-profile wlan-ssid [AC-wlan-vap-prof-wlan-vap] authentication-profile p1 [AC-wlan-vap-prof-wlan-vap] quit
# Bind the VAP profiles to the AP group and apply the VAP profiles to radio 0 and radio 1 of the APs.
[AC-wlan-view] ap-group name ap-group1 [AC-wlan-ap-group-ap-group1] vap-profile wlan-vap wlan 1 radio 0 [AC-wlan-ap-group-ap-group1] vap-profile wlan-vap wlan 1 radio 1 [AC-wlan-ap-group-ap-group1] quit
- Commit the configuration.
[AC-wlan-view] commit all Warning: Committing configuration may cause service interruption, continue?[Y/N]:y
- Verify the configuration.
The WLAN with the SSID wlan-net is available for STAs after the configuration is complete.
- The STAs obtain IP addresses when they successfully associate with the WLAN.
- When a user opens the browser and attempts to access the network, the user is automatically redirected to the authentication page provided by the Portal server. After entering the correct user name and password on the page, the user can access the network.
Configuration Files
SwitchA configuration file
# sysname SwitchA # vlan batch 100 # interface GigabitEthernet0/0/1 port link-type trunk port trunk pvid vlan 100 undo port trunk allow-pass vlan 1 port trunk allow-pass vlan 100 stp edged-port enable port-isolate enable group 1 # interface GigabitEthernet0/0/2 port link-type trunk undo port trunk allow-pass vlan 1 port trunk allow-pass vlan 100 # return
AC configuration file
# sysname AC # vlan batch 100 to 101 # authentication-profile name p1 portal-access-profile web1 free-rule-template default_free_rule authentication mode multi-authen max-user 100 access-domain huawei.com force # dhcp enable # radius-server template rd1 radius-server shared-key cipher %^%#4*SO-2u,Q.\1C~%[eiB77N/^2wME;6t%6U@qAJ9:%^%# radius-server authentication 10.23.2.30 1812 weight 80 # free-rule-template name default_free_rule free-rule 1 destination ip 10.23.3.1 mask 255.255.255.255 # web-auth-server abc server-ip 10.23.2.30 port 50200 shared-key cipher %^%#CR@WPM9Q30%]A}9]g4hUqe1u~4Fz}PlU)QPL;73#%^%# url http://10.23.2.30:8080/webagent # portal-access-profile name web1 web-auth-server abc direct # aaa authentication-scheme abc authentication-mode radius domain huawei.com authentication-scheme abc radius-server rd1 # interface Vlanif100 ip address 10.23.1.1 255.255.255.0 dhcp select interface # interface Vlanif101 ip address 10.23.2.1 255.255.255.0 dhcp select interface # interface GigabitEthernet1/0/1 port link-type trunk undo port trunk allow-pass vlan 1 port trunk allow-pass vlan 100 # interface GigabitEthernet1/0/2 port link-type trunk undo port trunk allow-pass vlan 1 port trunk allow-pass vlan 101 # wlan security-profile name wlan-security ssid-profile name wlan-ssid ssid wlan-net vap-profile name wlan-vap forward-mode tunnel service-vlan vlan-id 101 ssid-profile wlan-ssid security-profile wlan-security authentication-profile p1 regulatory-domain-profile name domain1 ap-group name ap-group1 regulatory-domain-profile domain1 radio 0 vap-profile wlan-vap wlan 1 radio 1 vap-profile wlan-vap wlan 1 ap-id 0 type-id 35 ap-mac 60de-4476-e360 ap-sn 210235554710CB000042 ap-name area_1 ap-group ap-group1 # return