Example for Configuring L2TP Load Balancing
This section provides an example for configuring load balancing among L2TP tunnels.
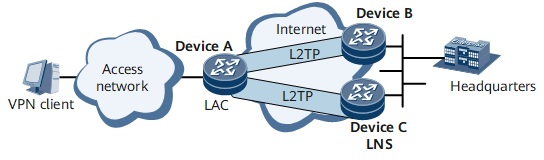
Networking Requirements
A single LNS sometimes cannot transmit all L2TP services due to performance limitation. To resolve this issue, L2TP load balancing can be enabled to distribute L2TP services among multiple LNSs based on LNS weights, as shown in Figure 1.
Configuration Roadmap
The configuration roadmap is as follows:
Configure a dial-up connection on the user side.
Configure the LAC. When configuring L2TP connections on the LAC, specify two LNS IP addresses for load balancing.
Configure the LNSs.
Data Preparation
To complete the configuration, you need the following data:
Username and password of PC1
Tunnel password, tunnel names on the LNSs, and tunnel name on the LAC
Virtual template numbers and L2TP group numbers
Number, range, and address mask of the remote address pool

This section provides only the procedures relevant to L2TP.
Procedure
- Configure a dial-up connection on the user side.
To create a dial-up connection, dial the Device A access number for receiving the addresses assigned by LNSs.
Enter the username user1@isp1 and the password (already registered on the LNSs) in the displayed dial-up terminal window on PC1.
- Configure Device A (LAC).
# Create a virtual template and configure a PPP authentication mode for it.
<Device> system-view [Device] sysname DeviceA [*DeviceA] interface virtual-template 1 [*DeviceA-Virtual-Template1] ppp authentication-mode chap [*DeviceA-Virtual-Template1] commit [~DeviceA-Virtual-Template1] quit
# Bind virtual template 1 to GE 0/1/8.100.
[~DeviceA] interface gigabitethernet 0/1/8.100 [*DeviceA-GigabitEthernet0/1/8.100] pppoe-server bind virtual-template 1 [*DeviceA-GigabitEthernet0/1/8.100] user-vlan 1 100 [*DeviceA-GigabitEthernet0/1/8.100-vlan-1-100] commit [~DeviceA-GigabitEthernet0/1/8.100-vlan-1-100] quit
# Configure BAS.
[~DeviceA-GigabitEthernet0/1/8.100] bas [*DeviceA-GigabitEthernet0/1/8.100-bas] access-type layer2-subscriber [*DeviceA-GigabitEthernet0/1/8.100-bas] authentication-method ppp [*DeviceA-GigabitEthernet0/1/8.100-bas] commit [~DeviceA-GigabitEthernet0/1/8.100-bas] quit [~DeviceA-GigabitEthernet0/1/8.100] quit
# Create a loopback interface.
[~DeviceA] interface loopback0 [*DeviceA-LoopBack0] ip address 1.1.1.1 255.255.255.255 [*DeviceA-LoopBack0] commit [~DeviceA-LoopBack0] quit
# Assign IP addresses to the physical interfaces of the tunnels.
[~DeviceA] interface gigabitethernet0/1/1 [*DeviceA-GigabitEthernet0/1/1] ip address 11.11.11.1 255.255.255.0 [*DeviceA-GigabitEthernet0/1/1] commit [~DeviceA-GigabitEthernet0/1/1] quit [~DeviceA] interface gigabitethernet0/1/2 [*DeviceA-GigabitEthernet0/1/2] ip address 12.12.12.1 255.255.255.0 [*DeviceA-GigabitEthernet0/1/2] commit [~DeviceA-GigabitEthernet0/1/2] quit
# Configure an L2TP group, set up L2TP tunnel connections for load balancing, and specify L2TP attributes.
[~DeviceA] l2tp enable [*DeviceA] commit [~DeviceA] l2tp-group lac1 [*DeviceA-l2tp-lac1] tunnel name lac1 [*DeviceA-l2tp-lac1] start l2tp ip 3.3.3.3 [*DeviceA-l2tp-lac1] start l2tp ip 4.4.4.4 [*DeviceA-l2tp-lac1] tunnel load-sharing [*DeviceA-l2tp-lac1] tunnel authentication [*DeviceA-l2tp-lac1] tunnel password cipher root@123 [*DeviceA-l2tp-lac1] tunnel source loopback0 [*DeviceA-l2tp-lac1] commit [~DeviceA-l2tp-lac1] quit
# Configure a RADIUS server group.
[~DeviceA] radius-server group radius1 [*DeviceA-radius-radius1] radius-server authentication 10.20.20.1 1812 [*DeviceA-radius-radius1] radius-server accounting 10.20.20.1 1813 [*DeviceA-radius-radius1] radius-server shared-key itellin [*DeviceA-radius-radius1] commit [~DeviceA-radius-radius1] quit
# Configure a user access domain.
[~DeviceA] aaa [*DeviceA-aaa] domain isp1 [*DeviceA-aaa-domain-isp1] l2tp-group lac1 [*DeviceA-aaa-domain-isp1] radius-server group radius1 [*DeviceA-aaa-domain-isp1] authentication-scheme default1 [*DeviceA-aaa-domain-isp1] accounting-scheme default1 [*DeviceA-aaa-domain-isp1] commit [~DeviceA-aaa-domain-isp1] quit
# Configure static routes to the LNSs.
[~DeviceA] ip route-static 3.3.3.3 255.255.255.255 11.11.11.2 [~DeviceA] ip route-static 4.4.4.4 255.255.255.255 12.12.12.2
- Configure Device B (LNS)
# Create Loopback 0.
[~DeviceB] interface loopback0 [*DeviceB-LoopBack0] ip address 3.3.3.3 255.255.255.255 [*DeviceB-LoopBack0] commit [~DeviceB-LoopBack0] quit
# Assign an IP address to the physical interface of the tunnel.
[~DeviceB] interface gigabitethernet0/1/1 [*DeviceB-GigabitEthernet0/1/1] ip address 11.11.11.2 255.255.255.0 [*DeviceB-GigabitEthernet0/1/1] commit [~DeviceB-GigabitEthernet0/1/1] quit
# Create a virtual template and configure a PPP authentication mode for it.
[~DeviceB] interface virtual-template 1 [*DeviceB-Virtual-Template1] ppp authentication-mode chap [*DeviceB-Virtual-Template1] commit [~DeviceB-Virtual-Template1] quit
# Enable L2TP and configure an L2TP group.
[~DeviceB] l2tp enable [*DeviceB] commit [~DeviceB] l2tp-group lns1 [*DeviceB-l2tp-lns1] tunnel name lns1 [*DeviceB-l2tp-lns1] allow l2tp virtual-template 1 remote lac1 [*DeviceB-l2tp-lns1] tunnel authentication [*DeviceB-l2tp-lns1] tunnel password cipher root@123 [*DeviceB-l2tp-lns1] commit [~DeviceB-l2tp-lns1] quit
# Create an LNS group named group1, and bind the tunnel board and tunnel interface to the LNS group.
[~DeviceB] lns-group group1 [*DeviceB-lns-group-group1] bind slot 1 [*DeviceB-lns-group-group1] bind source loopback 0 [*DeviceB-lns-group-group1] commit [~DeviceB-lns-group-group1] quit
# Configure an address pool used to assign an address to the user.
[~DeviceB] ip pool pool1 bas local [*DeviceB-ip-pool-pool1] gateway 10.10.0.1 255.255.255.0 [*DeviceB-ip-pool-pool1] section 0 10.10.0.10 10.10.0.100 [*DeviceB-ip-pool-pool1] commit [~DeviceB-ip-pool-pool1] quit
# Configure a RADIUS server group.
[~DeviceB] radius-server group radius1 [*DeviceB-radius-radius1] radius-server authentication 10.10.0.249 1812 [*DeviceB-radius-radius1] radius-server accounting 10.10.0.249 1813 [*DeviceB-radius-radius1] radius-server shared-key itellin [*DeviceB-radius-radius1] commit [~DeviceB-radius-radius1] quit
# Configure a user access domain.
[~DeviceB] aaa [*DeviceB-aaa] domain isp1 [*DeviceB-aaa-domain-isp1] authentication-scheme default1 [*DeviceB-aaa-domain-isp1] accounting-scheme default1 [*DeviceB-aaa-domain-isp1] radius-server group radius1 [*DeviceB-aaa-domain-isp1] ip-pool pool1 [*DeviceB-aaa-domain-isp1] commit [~DeviceB-aaa-domain-isp1] quit [~DeviceB-aaa] quit
# Configure a static route to the LAC.
[~DeviceB] ip route-static 1.1.1.1 255.255.255.255 11.11.11.1
- Configure Device C (LNS).
# Create a loopback interface.
[~DeviceC] interface loopback1 [*DeviceC-LoopBack1] ip address 4.4.4.4 255.255.255.255 [*DeviceC-LoopBack1] commit [~DeviceC-LoopBack1] quit
# Assign an IP address to the physical interface of the tunnel.
[~DeviceC] interface gigabitethernet0/1/1 [~DeviceC--GigabitEthernet0/1/1] ip address 12.12.12.2 255.255.255.0
# Create a virtual template and configure a PPP authentication mode for it.
[~DeviceC] interface virtual-template 1 [*DeviceC-Virtual-Template1] ppp authentication-mode chap [*DeviceC-Virtual-Template1] commit [~DeviceC-Virtual-Template1] quit
# Enable L2TP and configure an L2TP group.
[~DeviceC] l2tp enable [*DeviceC] commit [~DeviceC] l2tp-group lns1 [*DeviceC-l2tp-lns1] tunnel name lns1 [*DeviceC-l2tp-lns1] allow l2tp virtual-template 1 remote lac1 [*DeviceC-l2tp-lns1] tunnel authentication [*DeviceC-l2tp-lns1] tunnel password cipher root@123 [*DeviceC-l2tp-lns1] commit [~DeviceC-l2tp-lns1] quit
# Create an LNS group named group1 and bind the tunnel board and tunnel interface to the LNS group.
[~DeviceC] lns-group group1 [*DeviceC-lns-group-group1] bind slot 1 [*DeviceC-lns-group-group1] bind source loopback 1 [*DeviceC-lns-group-group1] commit [~DeviceC-lns-group-group1] quit
# Configure an address pool used to assign an address to the user.
[~DeviceC] ip pool pool1 bas local [*DeviceC-ip-pool-pool1] gateway 10.10.0.101 255.255.255.0 [*DeviceC-ip-pool-pool1] section 0 10.10.0.102 10.10.0.200 [*DeviceC-ip-pool-pool1] commit [~DeviceC-ip-pool-pool1] quit
# Configure a RADIUS server group.
[~DeviceC] radius-server group radius1 [*DeviceC-radius-radius1] radius-server authentication 10.10.0.249 1812 [*DeviceC-radius-radius1] radius-server accounting 10.10.0.249 1813 [*DeviceC-radius-radius1] radius-server shared-key itellin [*DeviceC-radius-radius1] commit [~DeviceC-radius-radius1] quit
# Configure a user access domain.
[~DeviceC] aaa [*DeviceC-aaa] domain isp1 [*DeviceC-aaa-domain-isp1] authentication-scheme default1 [*DeviceC-aaa-domain-isp1] accounting-scheme default1 [*DeviceC-aaa-domain-isp1] radius-server group radius1 [*DeviceC-aaa-domain-isp1] ip-pool pool1 [*DeviceC-aaa-domain-isp1] commit [~DeviceC-aaa-domain-isp1] quit [~DeviceC-aaa] quit
# Configure a static route to the LAC.
[~DeviceC] ip route-static 1.1.1.1 255.255.255.255 12.12.12.1
- Verify the configuration.
[~DeviceA] test l2tp-tunnel l2tp-group lac1 ip-address 3.3.3.3 Testing L2TP tunnel connectivity now....... Test L2TP tunnel connectivity success. [~DeviceA] test l2tp-tunnel l2tp-group lac1 ip-address 4.4.4.4 Testing L2TP tunnel connectivity now....... Test L2TP tunnel connectivity success.
Configuration Files
Device A configuration file
# sysname DeviceA # l2tp enable # radius-server group radius1 radius-server authentication 10.20.20.1 1812 radius-server accounting 10.20.20.1 1813 radius-server shared-key %^%#vS%796FO7%C~pB%CR=q;j}gSCqR-X6+P!.DYI@)%^% # interface Virtual-Template1 ppp authentication-mode chap # interface GigabitEthernet0/1/8.100 pppoe-server bind Virtual-Template 1 undo shutdown user-vlan 1 100 bas access-type layer2-subscriber # interface LoopBack0 ip address 1.1.1.1 255.255.255.255 # l2tp-group lac1 tunnel password cipher %@%##!!!!!!!!!"!!!!"!!!!(!!!!1];16qfZ81fv"uMoKKZ.1k"`AO!X2K2N.b~'NB^V!!!!!!!!!!1!!!!o/4J(q"J1F.!K9%M!6x8%@%# tunnel name lac1 start l2tp ip 3.3.3.3 start l2tp ip 4.4.4.4 tunnel load-sharing tunnel source LoopBack0 # aaa domain isp1 authentication-scheme default1 accounting-scheme default1 radius-server group radius1 l2tp-group lac1 # interface GigabitEthernet0/1/1 undo shutdown ip address 11.11.11.1 255.255.255.0 # interface GigabitEthernet0/1/2 undo shutdown ip address 12.12.12.1 255.255.255.0 # ip route-static 3.3.3.3 255.255.255.255 11.11.11.2 ip route-static 4.4.4.4 255.255.255.255 12.12.12.2 # return
Device B configuration file
# sysname DeviceB # l2tp enable # interface Virtual-Template1 ppp authentication-mode chap # interface LoopBack0 ip address 3.3.3.3 255.255.255.255 # l2tp-group lns1 allow l2tp virtual-template 1 remote lac1 tunnel password cipher %@%##!!!!!!!!!"!!!!"!!!!(!!!!1];16qfZ81fv"uMoKKZ.1k"`AO!X2K2N.b~'NB^V!!!!!!!!!!1!!!!o/4J(q"J1F.!K9%M!6x8%@%# tunnel name lns1 # lns-group group1 bind slot 1 bind source LoopBack0 # ip pool pool1 bas local gateway 10.10.0.1 255.255.255.0 section 0 10.10.0.2 10.10.0.100 # aaa domain isp1 authentication-scheme default1 accounting-scheme default1 ip-pool pool1 # interface GigabitEthernet0/1/1 undo shutdown ip address 11.11.11.2 255.255.255.0 # ip route-static 1.1.1.1 255.255.255.255 11.11.11.1 # return
Device C configuration file
# sysname DeviceC # l2tp enable # interface Virtual-Template1 ppp authentication-mode chap # interface LoopBack1 ip address 4.4.4.4 255.255.255.255 # l2tp-group lns1 allow l2tp virtual-template 1 remote lac1 tunnel password cipher %@%##!!!!!!!!!"!!!!"!!!!(!!!!1];16qfZ81fv"uMoKKZ.1k"`AO!X2K2N.b~'NB^V!!!!!!!!!!1!!!!o/4J(q"J1F.!K9%M!6x8%@%# tunnel name lns1 # lns-group group1 bind slot 1 bind source LoopBack1 # ip pool pool1 bas local gateway 10.10.0.101 255.255.255.0 section 0 10.10.0.102 10.10.0.200 # aaa domain isp1 authentication-scheme default1 accounting-scheme default1 ip-pool pool1 # interface GigabitEthernet0/1/1 undo shutdown ip address 12.12.12.2 255.255.255.0 # ip route-static 1.1.1.1 255.255.255.255 12.12.12.1 # return